Platform Security: Why Account Security Is Becoming a Priority for Platform Operators
- Reading time:
- 7 min

1. Account takeover is more than just an isolated problem
1.1 Account takeover attacks and their background
Account takeover refers to the unauthorized takeover of an online account. Attackers log in using someone else’s credentials and then act on behalf of the actual account holders: they place orders, change delivery addresses, cancel subscriptions, post content, send messages, or initiate further fraudulent activities.
The consequences initially affect the users involved. Depending on the platform, however, payments, personal data, business relationships, internal information, or a person’s digital reputation may also be affected. We have already reported on the general consequences of account takeover here.
The most common entry point is compromised login credentials, usually a combination of an email address and password. Such data can be leaked through phishing, malware, or so-called stealer logs. They are then traded on underground forums, automatically tested, and used for credential stuffing attacks.
1.2 Why Platforms Are Particularly Vulnerable
Large platforms are particularly attractive to attackers. Social media platforms, online shops, customer portals, and business platforms hold many user accounts, vast amounts of data, and numerous opportunities for action in one place. This creates effects of scale: A single successful login can be exploited for fraud, spam, phishing, fake reviews, data exfiltration, or further account takeovers.
These effects turn account takeover into a platform-level risk. Attackers often do not select their targets based on particular individuals, but instead automatically test large volumes of leaked credentials against known services. If a login is successful, they then assess the account’s value and how it can be further exploited.
The trust effect is particularly dangerous here. Messages, orders, or invitations from a genuine user account appear more credible than anonymous attacks from outside. A compromised account can thus deceive other users and trigger the next wave of attacks.
1.3 The Consequences for Platform Operators
When a large number of user accounts are compromised, the damage isn’t limited to users alone. The platform itself is put under pressure.
First of all, the support team has more work! Affected users need help with password changes, refunds, account suspensions, identity verification, and account recovery. Even a moderate wave of attacks can place a heavy burden on support teams.
Second, there is a risk of direct costs. In e-commerce, this can lead to unauthorized orders, purchases on account, vouchers, chargebacks, and goodwill cases. On business platforms, compromised accounts can also disrupt operational processes or expose sensitive information.
Third, reputation suffers. A platform where account takeovers occur with visible frequency loses trust. Users become more cautious, use core features less, or, when in doubt, switch to a provider they believe offers greater security.
2. Platform Security: Protecting Users Protects the Platform
2.1 What Platform Security Means
Platform security describes the systematic safeguarding of a digital platform against damage resulting from compromised user accounts. The term broadens the perspective: it is not just about protecting individual users from account takeover, but about protecting the platform as a whole from the consequences of mass account abuse.
This makes account security a core component of platform security. Platform protection encompasses technical, organizational, and procedural measures that enable operators to detect compromised credentials early on, prevent unauthorized logins, contain waves of attacks, and reduce collateral damage.
The central idea is this: user accounts are part of a platform’s security architecture. When they are compromised, they themselves become a vector for attack. Platform protection addresses this very issue.
2.2 Why User-Centric Measures Alone Are Not Enough
Traditional security measures often focus on the user. These include strong passwords, password managers, two-factor authentication, passkeys, and biometric authentication. These measures are important and should be supported.
However, they are not enough on their own. Not every user activates additional security measures. Some measures increase friction in the login process. And even highly security-conscious users can fall victim to phishing, malware, or data breaches at other services.
Platform operators should therefore not wait for every user to fully resolve their own account security. They need their own protection mechanisms that operate in the background and detect compromised credentials before any damage occurs.
The BSI IT-Grundschutz module ORP.4 emphasizes the detection of compromised passwords in ORP.4.A23:
Measures MUST be taken to detect compromised passwords.
For platform operators, this is not just a matter of compliance or consumer protection. It is in their own economic interest: Fewer compromised accounts mean fewer cases of fraud, less support burden, and greater trust in the platform.
2.3 Components of Effective Platform Security
Effective platform security combines multiple layers.
First, platforms should offer secure authentication methods. These include modern password policies, multi-factor authentication, passkeys, and clear recovery processes. These measures strengthen individual accounts but should not unnecessarily complicate their use.
Second, risk-based detection is needed. Suspicious login patterns, new devices, unusual locations, high error rates, or automated access attempts can indicate abuse. Such signals are valuable but often remain heuristic: they indicate a risk but do not always prove that an account has been compromised.
Third, compromised credentials should be actively detected. This is precisely where checking credentials against current leak data comes into play. If a platform learns that a user’s credentials have appeared in criminal databases, it can respond before attackers exploit this data.
3. From Reaction to Prevention: How Identeco Enables Platform Protection
3.1 Detecting Compromised Accounts Early
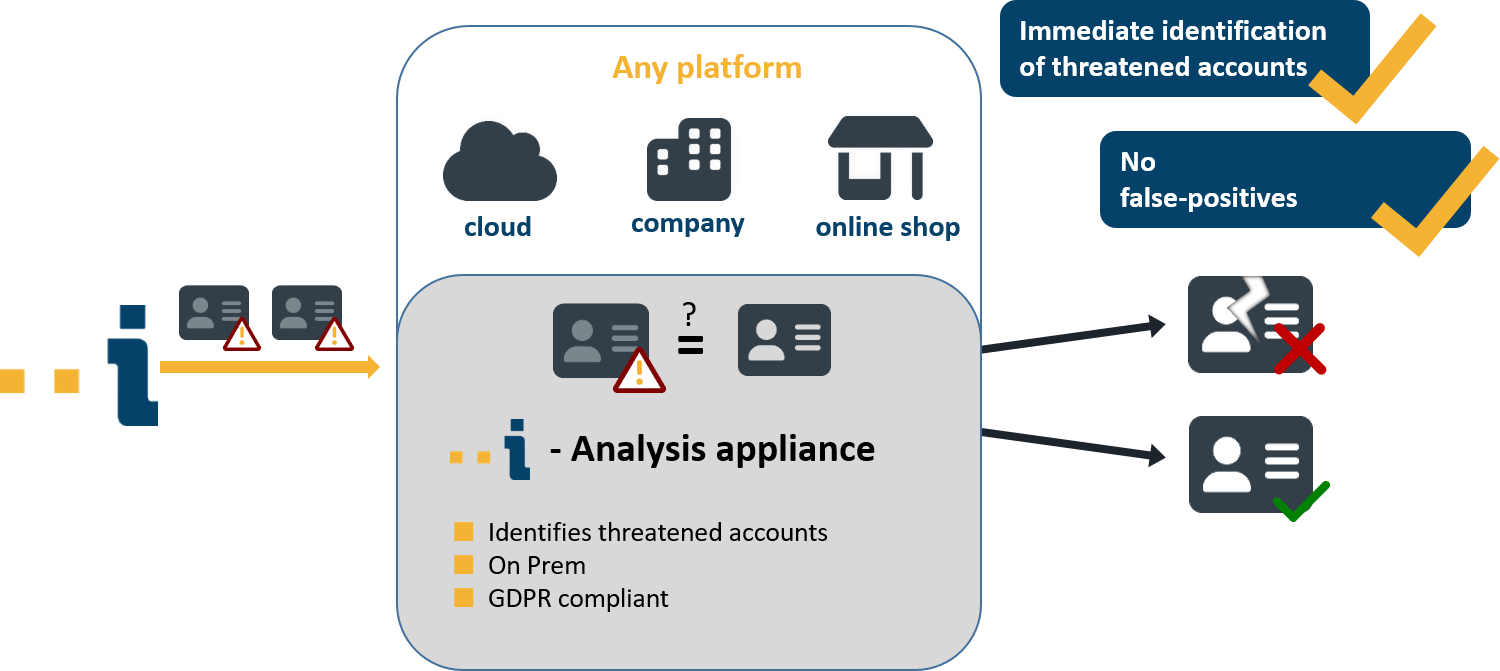
Identeco automatically detects over 300 million leaked credentials every month and processes them in compliance with data protection regulations. This information can help platforms identify and protect at-risk user accounts at an early stage.
Two use cases are particularly relevant here. In a live feed scenario, newly detected compromised credentials are continuously cross-referenced with a platform’s accounts. Affected accounts can then be flagged, protected, or prompted to change their passwords to a secure one.
In the login context, a credential check can also be performed directly during critical events, such as a login attempt or a security-related account change. This allows the system to determine whether the credentials being used are already known from a data breach. Depending on the risk, the platform can block the login, require additional verification, or secure the account.
This transforms reactive damage control into proactive platform protection.
3.2 Platform Protection as a Competitive Advantage
Platform protection isn’t just a nice-to-have feature—it’s a competitive advantage. Users trust platforms that reliably protect their accounts and act quickly when security risks arise.
For platform operators, this pays off in multiple ways. Fewer account takeovers mean fewer support cases, lower fraud costs, less reputational damage, and more stable user relationships. This difference is particularly noticeable for online stores, marketplaces, social media platforms, and business portals.
At the same time, platform protection strengthens brand integrity. A platform that detects compromised accounts early and prevents abuse demonstrates responsibility for its digital ecosystem. This builds trust among users, business partners, and internal stakeholders.
Conclusion
Account takeover is not an isolated user problem, but a systemic risk for platforms. Compromised login credentials are tested on a massive scale and can strain a platform operator’s support systems, fraud prevention efforts, reputation, and revenue.
That is why platform protection is essential: a proactive security approach that treats user accounts as an integral part of the platform architecture and detects compromised login credentials at an early stage.
Those who take platform protection seriously are not just protecting individual accounts. They are protecting trust, operational stability, and the platform’s economic foundation.
You can find more information on the topics discussed here:
Do you have further questions about data security, account security, or Identeco’s services? Feel free to contact us via email or schedule an appointment with us.


Artikel teilen